AI Defense against Internal Threats to Your Contact Center
Rulebase helps BPO contact centers combat internal fraud with advanced risk management. We enhance operational integrity and safeguard sensitive customer data by mitigating employee- and location-level threats.
Introduction
Rulebase is committed to addressing the growing challenge of internal fraud in contact centers, primarily focusing on Business Process Outsourcing (BPO) operations in the Philippines. As a global hub for outsourcing, the Philippines' contact centers handle customer communications across multiple channels such as phone calls, live chats, email, social media, and SMS, making them prime targets for cybercriminals. These bad actors exploit agents and weak authentication processes to access sensitive customer information. The consequences include financial losses, identity theft, and severe company reputation damage.
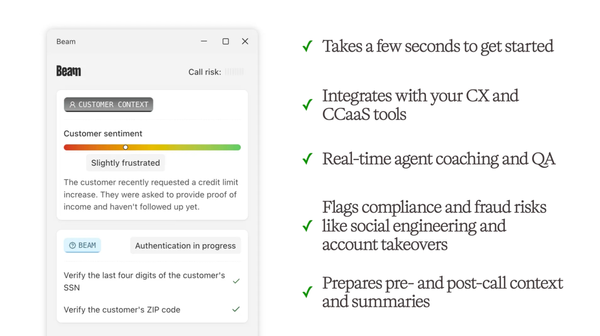
Our AI-powered defense system is designed to detect and block internal threats like employee collusion and data theft and external attacks such as impersonations and account takeovers (ATOs) within a single platform. Rulebase helps modern contact centers track unauthorized access, ATO calls, and high-risk behaviors, delivering real-time alerts and centralized threat visibility.
The Challenge: Internal Fraud in Contact Centers
Internal fraud in contact centers manifests in various ways, including unauthorized data access, misuse of client information, and employee collusion. Fraudsters increasingly exploit vulnerabilities in call centers through identity theft, account takeovers, and phishing scams. Agents, often the first line of defense, are targeted due to weak authentication systems and inadequate training, exposing organizations to significant financial and reputational risks.
The implications of these fraudulent activities are far-reaching. Beyond monetary losses, companies face the erosion of customer trust, potential legal liabilities, and operational disruptions. The shift to remote and hybrid work environments post-pandemic has only amplified these issues as organizations struggle to maintain practical fraud detection training and oversight.
Internal fraud cases often involve employees exploiting their access to sensitive information for personal gain or colluding with external actors. These actions include unauthorized data access, misuse of customer information, or bypassing security protocols to enable fraudulent transactions. Such insider activities are particularly challenging to detect due to the inherent trust in employees and the complexity of uncovering collusion schemes. Addressing these threats requires proactive monitoring and a deep understanding of behavior patterns within the organization.
These threats are particularly acute in the Philippines, a global BPO hub employing over 1.7 million individuals as of 2023. A 2022 Kroll report highlights that 75% of organizations in the Philippines experienced a cyber incident—a rate significantly higher than the Asia-Pacific average of 59%. Among the most common issues were data loss (70%) and threats to intellectual property (60%), both of which underscore the severity of insider threats.
Without proactive measures, the industry risks undermining its global standing. The IT and Business Process Association of the Philippines (IBPAP) warns that cybersecurity lapses, including insider fraud, threaten the sector’s ambitious goals of creating 1.1 million jobs and generating $59 billion in export revenue by 2028. For the Philippines to retain its position as a preferred outsourcing destination, robust strategies to mitigate internal fraud must become a cornerstone of the industry’s operational framework.
The Solution: Risk-Based Insider Fraud Detection
The Rulebase fraud detection framework combines risk rules, alerts, and scoring systems to aggregate and monitor risk levels for employees and locations. The system generates a comprehensive risk profile by analyzing events such as unauthorized access, flagged calls, and social media activity. This enables centralized monitoring and real-time threat visibility across the organization.
Example 1: Unauthorized Data Access
Typical Scenario: Outside of any active communication with a customer, an agent accesses a customer account to view sensitive information. This could be an intentional act to misuse data or a careless action that still exposes the company to significant compliance risks.
How Rulebase Helps: Rulebase integrates seamlessly with IVR and call center systems to monitor account access activities continuously. The system automatically flags this as a potential violation when an agent attempts to access a customer account without any ongoing call or text conversation. These events are evaluated for severity, logged into the agent's risk profile, and presented to supervisors with actionable insights.
Example 2: High-Risk Calls
Typical Scenario: A customer call raises red flags for impersonation or account takeover (ATO) attempts, such as mismatched caller information, suspicious requests for account changes, or patterns resembling known fraud tactics. These calls pose significant risks to the business and its customers if not identified early.
How Rulebase Helps: Rulebase employs advanced AI to analyze call metadata and content, identifying calls that exhibit high-risk behaviors. For instance, the system detects discrepancies in authentication patterns, unusual account activity requests, or voice characteristics suggesting impersonation. These flagged calls are escalated with severity scores and linked to the agent handling them, enabling supervisors to investigate further.
Example 3: Social Media and Dark Web Monitoring
Typical Scenario: A disgruntled employee posts disparaging or confidential information about the company, its clients, or employees on public platforms like LinkedIn or Facebook. Simultaneously, mentions of company or employee details appear on dark web forums, potentially signaling insider threats or preparations for fraud. These actions jeopardize the company’s reputation and expose sensitive data.
How Rulebase Helps: Rulebase employs AI-powered tools to monitor social media platforms and dark web channels for mentions of the business, its clients, and its employees. On social media, sentiment analysis and keyword tracking identify posts tied to confidentiality breaches, complaints, or brand disparagement. For dark web activity, Rulebase scans forums and marketplaces for indicators of potential fraud, such as leaked customer data or insider collusion.
By associating flagged incidents with specific employees or locations, Rulebase provides actionable insights for risk mitigation.
Conclusion
Internal fraud poses a significant threat to contact centers. Organizations can effectively mitigate these risks and protect their business operations by implementing a robust risk management framework.
Contact us directly for more information or to discuss how Rulebase can help your organization. Email founders@rulebase.co to speak with our founders and security experts to address your specific challenges and see Rulebase in action.