How to assess fraud risks within your BPO (and fix it in 7 days)

A massive shoutout to Brian D. I was inspired by a similar post.
Fraud in Business Process Outsourcing (BPO) isn’t just about stolen credit cards or phishing scams. It’s about insider threats, data leaks, and systemic vulnerabilities that can cripple client trust and trigger contract losses overnight. Here’s how to figure out where the gaps are and deliver actionable insights —without losing your sanity.
Step 1: Mine the last 90 days of data
Start by gathering everything:
- Security logs (failed logins, after-hours access)
- Incident reports (policy violations, data mishandling)
- Client complaints (fraudulent transactions traced to your team)
- HR records (disciplinary actions, sudden resignations)
Pro Tip: Sometimes you might not have access to customer logs, in those instances, focus on incident reports and looking through flagged calls to see if there are any recurring themes of access or specific culprits.
Step 2: Map every entry point of potential fraud
Focus on where data, money, or access flows:
- Client systems: CRM access, payment gateways, call recordings.
- Internal processes: Payroll approvals, vendor invoice routing.
- Physical risks: Unlocked workstations, unshredded documents.
Step 3: Talk to the frontline Teams.
Your agents, IT staff, and HR hold clues you’ll never find in logs. Ask:
- Agents: “Have you seen colleagues bypass security steps to hit KPIs?”
- IT: “Which systems have the weakest monitoring?”
- HR: “Any patterns in misconduct reports?”
Red Flags:
- We all use the same password for the billing tool—it’s faster!
- That project was phased out, but the vendor still has access.
Step 4: Build a risk heat map
Score each entry point on three factors:
- Impact: Financial loss, client churn, legal penalties.
- Likelihood: How easily could someone exploit this? Keep things simple: easy, medium, and hard.
- Detection Gap: How would you catch it today?
Example:
- High Risk: Agents with access to payroll and client payment systems.
- Low Risk: Read-only data access with multi-factor authentication (MFA).
Step 5: Stress-test your top 5 Risks
Run “What If?” scenarios:
- What if a disgruntled team lead exports 10,000 client records?
- What if a phishing email hijacks agent credentials?
Reality Check:
Your detection time and response protocols will likely horrify you. That’s the point.
Step 6: Audit your current controls
Compare your safeguards to the heat map. Brutal questions:
- Are you monitoring screen recordings for copy-pasted credit card data?
- Do you review access logs after employees quit?
- Are background checks skipped for specific agents, and do those agents have a higher ratio of incidents?
The Hard Truth:
Most BPOs overinvest in perimeter security (firewalls) and ignore insider threats (like agents selling data on Telegram).
Step 7: Build a 60-day action plan
Prioritize ruthlessly:
- Quick Wins: Disable USB drives and enforce session timeouts.
- Critical Fixes: Segregate financial system access and automate access revocation.
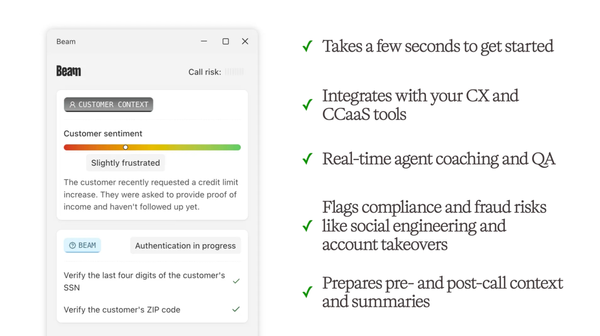
- Long-Term Plays: Deploy AI anomaly detection (e.g., unusual data downloads).
Leadership Hack:
Frame fixes as “client retention” strategies. Example:
“Securing payroll systems prevents $500K in annual fraud losses—and keeps Client X off our backs.”
Step 8: Sell your plan
Leadership won’t read a 50-page report. Give them:
- A Heat Map: Color-coded by risk level.
- Cost of Inaction: “One data leak = $4M (IBM’s avg. breach cost) + 2 lost clients. $50k in monitoring prevents $1m in losses.
Pro Move
Include a 30-second recording of an employee acting fraudulently, either through collaborating with an external lousy actor or any example to demonstrate what agents can do today.
Why this works
- Targets Insider Threats: A massive percentage of risks facing BPO stems from internal threats.
- Balances Speed & Security: No one wants to slow down call center ops—but you can’t ignore the ticking bombs.
- Aligns with Client Demands: Clients like Fortune 500 firms now audit BPOs for ISO 27001 and SOC 2 compliance.
Final Tip
Start with the easiest high-impact fix (e.g., killing shared logins) and announce it company-wide. Momentum is your best ally.
PS - Want to access a ready-made heatmap? Reach out to founders@rulebase.co to get our free BPO Fraud Risk Assessment Template.